Available translations: German, French, Spanish
We get it; securing your own bitcoins can be daunting. But it becomes easier once you understand a few basic principles. Not relying on a third party to safe-keep your funds is a paradigm shift, but we believe it’s possible for everyone and totally worth it. In this article, we’ll answer the most common questions we get from people new to the concept of hardware wallets.
Where are my coins actually stored?
Let’s start with the elephant in the room: are my coins stored in the wallet, or where the heck are they? This is an excellent question because the answer defines what your wallet actually needs to protect.
Cryptocurrencies are called like that because they are secured by cryptography. For this purpose, you need a set of digital keys, for example your (very secret) private key. With this key, you can encrypt and digitally sign things.
Now let’s take Bitcoin as an example (other cryptocurrencies work in a similar way). The whole Bitcoin network is kept in sync through a shared data structure, the blockchain. It contains records of all the transactions ever made and is publicly available online, so anyone can read it. If you receive some bitcoins, let’s say 0.1 BTC, you see them in your Bitcoin wallet, listed under a Bitcoin address.
Your bitcoins are not actually stored in the wallet, they’re just an entry in the public blockchain. What the wallet stores is your secret private key that belongs to that address. Because you control this private key, you can spend these bitcoins: this is how “Bitcoin ownership” is defined. Everybody can see these bitcoins, but only you can spend them, so they are yours. But this also means that *everyone* that has the right private key can spend these bitcoins. This is why it’s very important to keep this key a secret.
What are common threats to my bitcoins?
Bitcoin ownership is defined by having access to the private keys that allows you to spend them, and these keys need to be protected. But against what? What are some common threats to your coins?
Phishing: most common and successful
Did you ever receive an email from a “prince” somewhere, offering you money if you just help him out? That’s an obvious scam. But what if you’re not quite sure how Bitcoin works, and you receive a well-formatted email from your cryptocurrency exchange, asking you to confirm a few things? Be aware! This is called social engineering. It can be very subtle and many people fall for it.
Main takeaway: Never ever disclose your private keys or your wallet backup (a microSD card or 24 recovery words) to anyone, and never enter them on any device that is not a hardware wallet. Don’t trust anyone asking you to do this, even if they claim they’re an exchange or even the hardware wallet manufacturer.
Remote attacks: scale really well
Depending on the source, between 30% and 50% of computers have been infected with malicious software at some point. A virus could monitor your clipboard for Bitcoin addresses and replace them with the attacker's address. It could make your software wallet send your coins somewhere or steal your private keys. The problem with these attacks is that they scale very well: an attacker needs to write the code once, distribute it and then wait for the “rewards” to come in.
Main takeaway: Always assume that your computer or phone is compromised and could steal your coins. It's a similar situation with the wallet you use to store cash in your local currency: the risk is ok for a limited amount for daily use, but you wouldn’t keep your life savings in your back pocket.
Local attacks: take a lot of effort
Someone with physical access to your computer hardware or mobile phone could manipulate it to send out secrets, or they could physically threaten you to hand over your funds. Attacks like that happen, but are rare because they’re very targeted and need a lot of effort and criminal effort. The best prevention against that is to not brag about how many bitcoins you own and enable digital access controls for the devices you use.
Main takeaway: Take privacy seriously and don’t paint yourself a bull’s eye on your back in social media. Protect access to your devices and invest in a hardware wallet if you secure significant amounts.
What makes a hardware wallet secure?
So many attack vectors, but don’t fret. It’s important to understand what we’re up against, so can we come up with adequate protections. The main issue with regular computers or phones is that they’re just too complex to be secure. Any kind of update could undermine your security, and with millions of lines of code it’s impossible to know exactly what’s going on. Building a secure crypto storage on top of that is nearly impossible.
Hardware wallets like the BitBox02, on the other hand, are simple by design. They don’t have an operating system like Windows or MacOS, no background programs running, no “login” functionality. They are made with the sole purpose of protecting your private keys, and never to disclose them. A hardware wallet usually comes with a software companion app, like our BitBoxApp. You should always assume that your computer or phone is already compromised with malware, and with that in mind not even the BitBoxApp on your computer can be trusted. But that’s ok, because the application never learns any secrets.
Whenever you want to use cryptocurrencies, it’s the BitBoxApp that talks to the outside world, but only the BitBox02 hardware wallet does the secret stuff. These are the two important benefits of a hardware wallet:
- It creates your private keys directly on the device and keeps them safe from any unauthorized access, remote or local.
- It lets you independently verify and confirm important information on its secure screen because your computer or phone screen can be easily manipulated by malware.
Main takeaway: A special-purpose hardware wallet helps to keep our coins safe. Always trust the secure screen of your BitBox02 over what your computer or phone shows.
What if I lose my wallet?
Every wallet consists of two parts: the wallet itself and its backup. The primary purpose of a wallet is to keep your coins usable. That means securing your private keys while still having digital access to them. But computers can stop working, software can be deleted, smartphones can be lost and hardware wallets can be lost at sea.
If you lose your wallet, it's the backup's time to shine! Simply get a new BitBox02 and restore your wallet in minutes.
How did you create this backup? With the BitBox02 you write it to the included microSD card right when you set up the device. Other wallets make you write down 24 recovery words (which is an option on the BitBox02 as well).
Two essential things to know:
- The wallet backup is standardized and can be restored in any other modern wallet.
- It is also very sensitive and needs to be kept secure and separate from your hardware wallet. Read more about backup solutions.
Main takeaway: Make sure you have a verified backup and that it's secured properly.
Can a hardware wallet be hacked?
Yes, of course, everything can be hacked. If someone tells you otherwise, they either don’t understand that information security is a constant battle, or they’re simply lying. But: it’s possible to raise the cost and success rate of getting hacked to a level where it’s no longer feasible for an attacker.
The following security features of the BitBox02 make it one of the most secure hardware wallets. It is very hard to breach, and when doing so there is a high chance of physically destroying it in the process.
- Minimal software
Regular software has millions of lines of programming code and uses many ready-made libraries that are written by others. A secure system must run on minimal software that can be audited line-by-line. The BitBox02 Bitcoin-only edition takes this security principle to the next level: it can only run radically focused firmware for Bitcoin, no altcoins, no other “nice-to-have” features. - Restrictive communication interface
A hardware wallet must be very strict with answering requests by insecure computers. You can’t “log in” to a hardware wallet or access its memory like a USB thumbdrive. The BitBox02 uses a very restrictive communication protocol, and simply aborts an information exchange if the other side does not follow it exactly. - Secure hardware
To protect against local attacks, it is essential that a hardware wallet uses hardware especially designed against physical tampering. Without a secure chip, experts can just read out the secrets using specialized equipment. The BitBox02 uses a secure chip specifically built for physical device hardening. - Secure supply chain
Using a fake and potentially malicious hardware wallet is a serious risk. This is why the BitBox02 is engineered and manufactured in Switzerland, where we oversee the whole production process. The official BitBoxApp is able to detect if the BitBox02 is an original device to prevent users from getting bad clones. And the BitBox02 only runs official firmware signed by Shift Crypto so that nobody can load a malicious firmware on an otherwise real BitBox02 before you get it.
Ok, but what stops the manufacturer of your hardware from using a backdoor and just taking your coins? In the case of the BitBox02, how much do you need to trust us? While a fully “trustless” solution is probably not possible, we do everything we can to minimize your need to trust us. And this comes down to the following:
- Full transparency
The firmware on your hardware wallet has full access to your private keys and could do all sorts of malicious things. This is why the program code must be publicly available for review, and firmware updates need to be created to allow verification that the firmware is actually built from the public source code.
But not only is all our software fully open-source, we even publish everything there is to know about the hardware used, down to the individual components. - External audits
The BitBox02 firmware was audited by Census Labs along with consulting done by multiple third-party security firms. Plus, we encourage independent researchers to audit the BitBox02 on an ongoing basis, and we reward them through our bug-bounty program if they find anything. That does not limit their options to publish a full independent report without our permission.
Main takeaway: More is not always "better". Part of security is simplicity and full control of the supply chain. A wallet handles your secret private keys and needs full access to them. You can and should demand full transparency about how a wallet works and make sure that independent public audits are encouraged.
Our main goal is to empower every Bitcoin and cryptocurrency user, both by building products that keep your funds safe, as well as helping you find the information about how to do that best. Yes, securing your own bitcoins can be daunting, but we’d like to support you in your journey! We designed our BitBox02 and the companion BitBoxApp with exactly this in mind: making you feel comfortable when taking that first step and start using a hardware wallet.
Don’t own a BitBox yet?
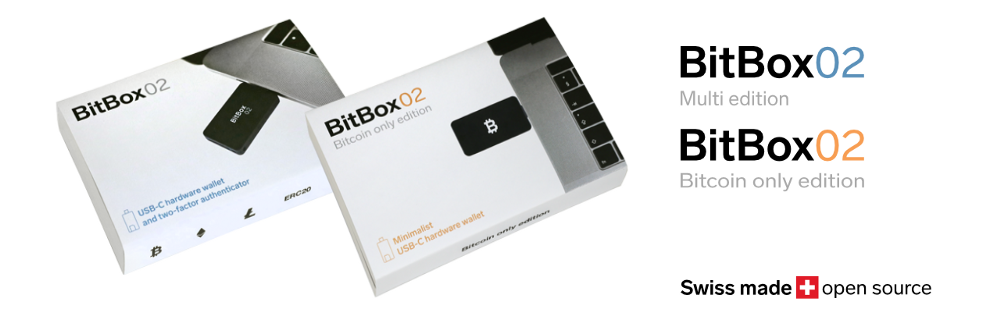
Keeping your crypto secure doesn't have to be hard. The BitBox02 hardware wallet stores the private keys for your cryptocurrencies offline. So you can manage your coins safely.
The BitBox02 also comes in Bitcoin-only version, featuring a radically focused firmware: less code means less attack surface, which further improves your security when only storing Bitcoin.
Frequently Asked Questions (FAQ)
Where are my bitcoin actually stored?
Your coins are not stored in the wallet; they're just an entry in the public blockchain. The wallet stores your secret private key that belongs to that address. Because you control this private key, you can spend these bitcoin.
What are common threats to my bitcoin?
Common threats include phishing, remote attacks, and local attacks. It's essential to never disclose your private keys, always assume your computer or phone is compromised, and take privacy seriously.
What makes a hardware wallet secure?
Hardware wallets are simple by design, without complex operating systems. They protect your private keys and never disclose them. They allow you to independently verify and confirm important information on a secure screen.
What if I lose my wallet?
If you lose your wallet, you can use your backup to restore it. The backup is either on a microSD card or written down as 24 recovery words.
Can a hardware wallet be hacked?
While everything can be hacked, hardware wallets like the BitBox02 have multiple security features that make it very hard to breach. It's essential to have full transparency about how a wallet works and ensure independent public audits.
Shift Crypto is a privately held company based in Zurich, Switzerland. Our international team of specialists across engineering, cryptosecurity and Bitcoin core development build the BitBox products and provide consulting services. The BitBox02, a second generation hardware wallet, equips individuals to easily store, protect, and transact cryptocurrencies. Its companion, the BitBoxApp, provides an all-in-one solution to securely manage your digital assets with ease.

